Microsoft on Thursday attributed the recent spate of ransomware incidents targeting transportation and logistics sectors in Ukraine and Poland to a threat cluster that shares overlaps with the Russian state-sponsored Sandworm group.
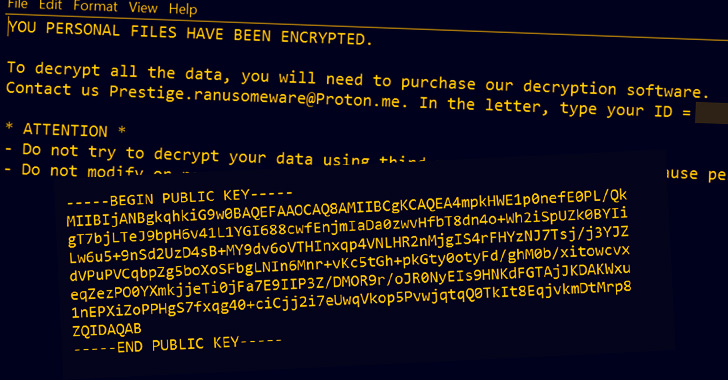
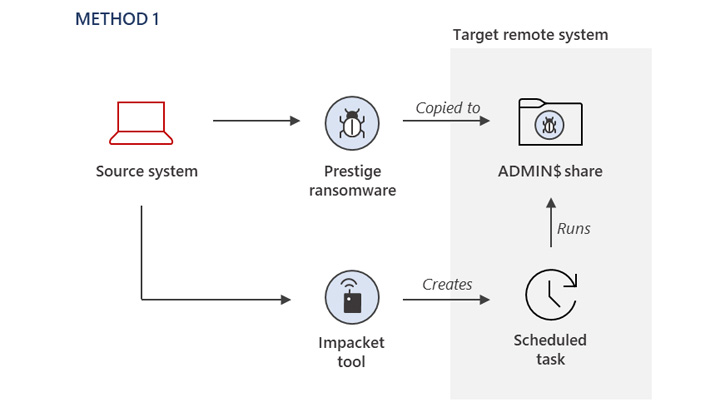
The attacks, which were disclosed by the tech giant last month, involved a strain of previously undocumented malware called Prestige and is said to have taken place within an hour of each other across all victims.
The Microsoft Threat Intelligence Center (MSTIC) is now tracking the threat actor under its element-themed moniker Iridium (née DEV-0960), citing overlaps with Sandworm (aka Iron Viking, TeleBots, and Voodoo Bear).
“This attribution assessment is based on forensic artifacts, as well as overlaps in victimology, tradecraft, capabilities, and infrastructure, with known Iridium activity,” MSTIC said in an update.
The company also further assessed the group to have orchestrated compromise activity targeting many of the Prestige victims as far back as March 2022, before culminating in the deployment of the ransomware on October 11.
The method of initial compromise still remains unknown, although it’s suspected that it involved gaining access to highly privileged credentials necessary to activate the killchain.
“The Prestige campaign may highlight a measured shift in Iridium’s destructive attack calculus, signaling increased risk to organizations directly supplying or transporting humanitarian or military assistance to Ukraine,” the company said.
The findings come over a month after Recorded Future linked another activity group (UAC-0113) with ties to the Sandworm actor as having singled out Ukrainian users by masquerading as telecom providers in the country to deliver backdoors onto compromised machines.
Microsoft, in its Digital Defense Report published last week, further called out Iridium for its pattern of targeting critical infrastructure and operational technology entities.
“Iridium deployed the Industroyer2 malware in a failed effort to leave millions of people in Ukraine without power,” Redmond said, adding the threat actor used “phishing campaigns to gain initial access to desired accounts and networks in organizations within and outside Ukraine.”
The development also arrives amid sustained ransomware attacks aimed at industrial organizations worldwide during the third quarter of 2022, with Dragos reporting 128 such incidents during the time period compared to 125 in the previous quarter.

“The LockBit ransomware family account for 33% and 35% respectively of the total ransomware incidents that target industrial organizations and infrastructures in the last two quarters, as the groups added new capabilities in their new LockBit 3.0 strain,” the industrial security firm said.
Other prominent strains observed in Q3 2022 include Cl0p, MedusaLocker, Sparta, BianLian, Donuts, Onyx, REvil, and Yanluowang.