New research has found that it is possible for threat actors to abuse a legitimate feature in GitHub Codespaces to deliver malware to victim systems.
GitHub Codespaces is a cloud-based configurable development environment that allows users to debug, maintain, and commit changes to a given codebase from a web browser or via an integration in Visual Studio Code.
It also comes with a port forwarding feature that makes it possible to access a web application that’s running on a particular port within the codespace directly from the browser on a local machine for testing and debugging purposes.
“You can also forward a port manually, label forwarded ports, share forwarded ports with members of your organization, share forwarded ports publicly, and add forwarded ports to the codespace configuration,” GitHub explains in its documentation.
It’s important to note here that any forwarded port that’s made public will also permit any party with knowledge of the URL and port number to view the running application sans any authentication.
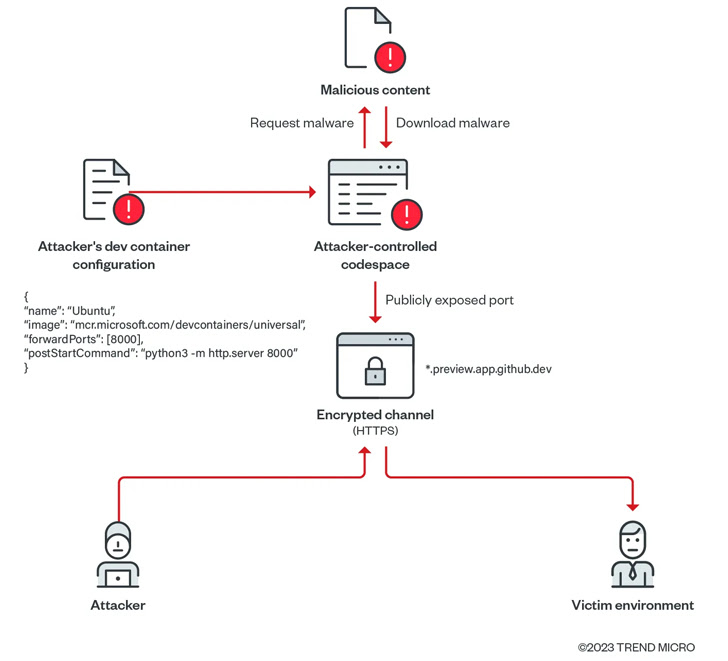
Furthermore, GitHub Codespaces uses HTTP for port forwarding. Should the publicly visible port be updated to use HTTPS or removed and re-added, the port’s visibility is automatically changed to private.
Cybersecurity firm Trend Micro found that such publicly-shared forwarded ports could be exploited to create a malicious file server using a GitHub account.
“In the process, these abused environments will not be flagged as malicious or suspicious even as it serves malicious content (such as scripts, malware, and ransomware, among others), and organizations may consider these events as benign or false positives,” researchers Nitesh Surana and Magno Logan said.
In a proof-of-concept (PoC) exploit demonstrated by Trend Micro, a threat actor could create a codespace and download malware from an attacker-controlled domain to the environment, and set the visibility of the forwarded port to public, essentially transforming the application to act as a web server hosting rogue payloads.
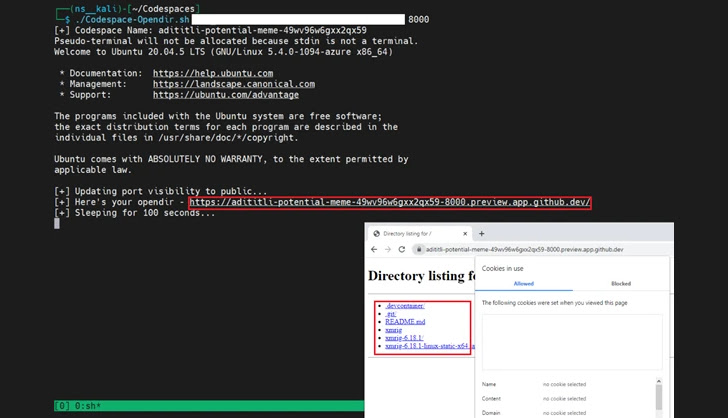
Even more troublingly, the adversary can augment this method to deploy malware and compromise a victim’s environment since each codespace domain associated with the exposed port is unique and unlikely to be flagged by security tools as a malicious domain.
“Using such scripts, attackers can easily abuse GitHub Codespaces in serving malicious content at a rapid rate by exposing ports publicly on their codespace environments,” the researchers explained.
While the technique is yet to be observed in the wild, the findings are a reminder as to how threat actors could weaponize cloud platforms to their benefit and carry out an array of illicit activities.
“Cloud services offer advantages to legitimate users and attackers alike,” the researchers concluded. “The features offered to legitimate subscribers also become available to threat actors as they take advantage of the resources provided by the [cloud service provider].”
