Researchers are warning about a spike in exploitation attempts weaponizing a critical remote code execution flaw in Realtek Jungle SDK since the start of August 2022.
According to Palo Alto Networks Unit 42, the ongoing campaign is said to have recorded 134 million exploit attempts as of December 2022, with 97% of the attacks occurring in the past four months.
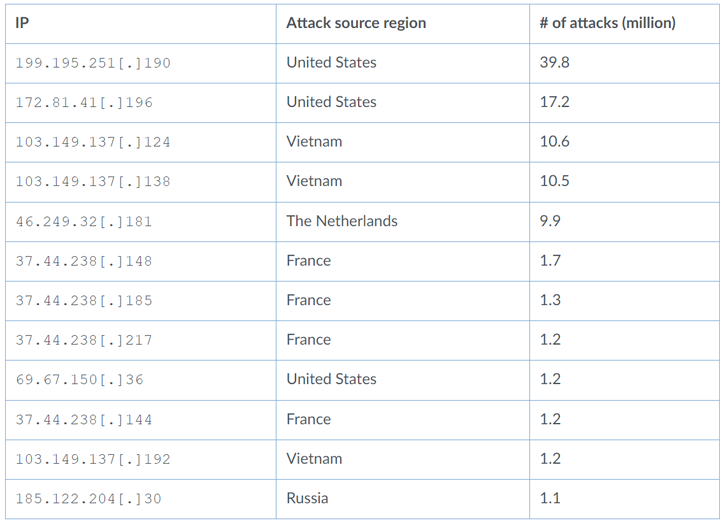
Close to 50% of the attacks originated from the U.S. (48.3%), followed by Vietnam (17.8%), Russia (14.6%), The Netherlands (7.4%), France (6.4%), Germany (2.3%0, and Luxembourg (1.6%).
What’s more, 95% of the attacks leveraging the security shortcoming that emanated from Russia singled out organizations in Australia.
“Many of the attacks we observed tried to deliver malware to infect vulnerable IoT devices,” Unit 42 researchers said in a report, adding “threat groups are using this vulnerability to carry out large-scale attacks on smart devices around the world.”
The vulnerability in question is CVE-2021-35394 (CVSS score: 9.8), a set of buffer overflows and an arbitrary command injection bug that could be weaponized to execute arbitrary code with the highest level of privilege and take over affected appliances.
The issues were disclosed by ONEKEY (previously IoT Inspector) in August 2021. The vulnerability impacts a wide range of devices from D-Link, LG, Belkin, Belkin, ASUS, and NETGEAR.
Unit 42 said it discovered three different kinds of payloads distributed as a result of in-the-wild exploitation of the flaw –
- A script executes a shell command on the targeted server to download additional malware
- An injected command that writes a binary payload to a file and executes it, and
- An injected command that directly reboots the targeted server to cause a denial-of-service (DoS) condition
Also delivered through the abuse of CVE-2021-35394 are known botnets like Mirai, Gafgyt, and Mozi, as well as a new Golang-based distributed denial-of-service (DDoS) botnet dubbed RedGoBot.
First observed in September 2022, the RedGoBot campaign involves dropping a shell script that’s designed to download a number of botnet clients tailored to different CPU architectures. The malware, once launched, is equipped to run operating system commands and mount DDoS attacks.
The findings once again underscore the importance of updating software in a timely fashion to avoid exposure to potential threats.
“The surge of attacks leveraging CVE-2021-35394 shows that threat actors are very interested in supply chain vulnerabilities, which can be difficult for the average user to identify and remediate,” the researchers concluded. “These issues can make it difficult for the affected user to identify the specific downstream products that are being exploited.”
