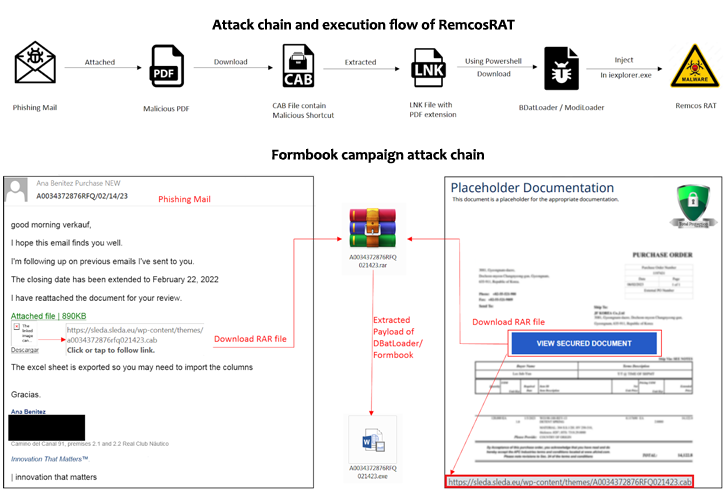
A new phishing campaign has set its sights on European entities to distribute Remcos RAT and Formbook via a malware loader dubbed DBatLoader.
“The malware payload is distributed through WordPress websites that have authorized SSL certificates, which is a common tactic used by threat actors to evade detection engines,” Zscaler researchers Meghraj Nandanwar and Satyam Singh said in a report published Monday.
The findings build upon a previous report from SentinelOne last month that detailed phishing emails containing malicious attachments that masquerade as financial documents to activate the infection chain.
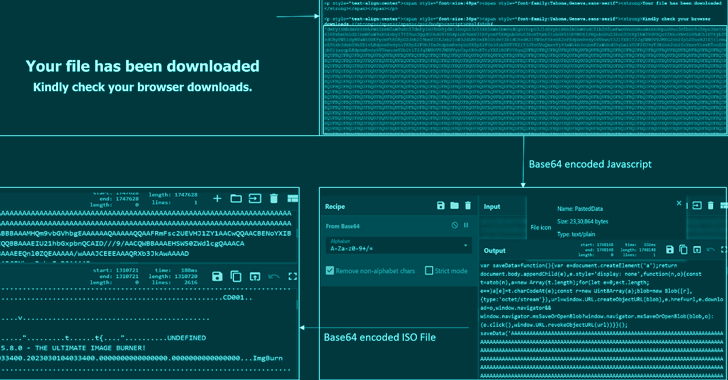
Some of the file formats used to distribute the DBatLoader payload concern the use of a multi-layered obfuscated HTML file and OneNote attachments.
The development adds to growing abuse of OneNote files as an initial vector for malware distribution since late last year in response to Microsoft’s decision to block macros by default in files downloaded from the internet.
DBatLoader, also called ModiLoader and NatsoLoader, is a Delphi-based malware that’s capable of delivering follow-on payloads from cloud services like Google Drive and Microsoft OneDrive, while also adopting image steganography techniques to evade detection engines.
One notable aspect of the attack is the use of mock trusted directories such as “C:\Windows \System32” (note the trailing space after Windows) to bypass User Account Control (UAC) and escalate privileges.
Discover the Hidden Dangers of Third-Party SaaS Apps
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions being granted and how to minimize risk.
RESERVE YOUR SEAT
A caveat here is that the directories cannot be directly created from within the Windows Explorer user interface, instead requiring the attacker to rely on a script to accomplish the task and copy to the folder a rogue DLL and a legitimate executable (easinvoker.exe) that’s vulnerable to DLL hijacking in order to load the DLL payload.
This enables the attackers to conduct elevated activities without alerting users, including establishing persistence and adding the “C:\Users” directory to the Microsoft Defender exclusion list to avoid getting scanned.
To mitigate risks posed by DBatLoader, it’s advised to monitor process executions that involve filesystem paths with trailing spaces and consider configuring Windows UAC to Always notify.