Human rights activists in Morocco and the Western Sahara region are the targets of a new threat actor that leverages phishing attacks to trick victims into installing bogus Android apps and serve credential harvesting pages for Windows users.
Cisco Talos is tracking the activity cluster under the name Starry Addax, describing it as primarily singling out activists associated with the Sahrawi Arab Democratic Republic (SADR).
Starry Addax’s infrastructure – ondroid[.]site and ondroid[.]store – is designed to target both Android and Windows users, with the latter involving fake websites masquerading as login pages for popular social media websites.
In light of active investigation into the campaign, Talos said it cannot publicly disclose which websites are being targeted with credential harvesting attacks.

“However, the threat actors are establishing their own infrastructure and hosting credential harvesting pages such as fake login pages for media and email services popular throughout the globe,” the company told The Hacker News.
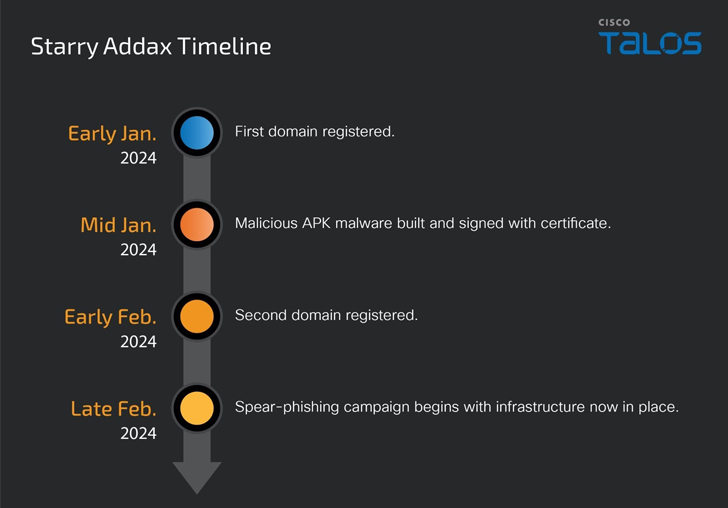
The adversary, believed to be active since January 2024, is known to send spear-phishing emails to targets, urging recipients to install Sahara Press Service’s mobile app or a relevant decoy related to the region.
Depending on the operating system from where the request is originating from, the target is either served a malicious APK that impersonates the Sahara Press Service or redirected to a social media login page to harvest their credentials.
The novel Android malware, dubbed FlexStarling, is versatile and equipped to deliver additional malware components and steal sensitive information from infected devices.
Once installed, it requests the victim to grant it extensive permissions that allow the malware to perform nefarious actions, including fetching commands to be executed from a Firebase-based command-and-control (C2), a sign that the threat actor is looking to fly under the radar.
“Campaigns like this that target high-value individuals usually intend to sit quietly on the device for an extended period,” Talos said.
“All components from the malware to the operating infrastructure seem to be bespoke/custom-made for this specific campaign indicating a heavy focus on stealth and conducting activities under the radar.”
The development comes amid the emergence of a new commercial Android remote access trojan (RAT) known as Oxycorat that’s being offered for sale with diverse information gathering capabilities.

The latest findings mark an interesting twist in that Starry Addax has taken pains to build its own arsenal of tools and infrastructure to target human rights activists as opposed to relying on commodity malware or commercially available spyware.
“The attacks are still in nascent stages, operationally. However, the supporting infrastructure and malware, FlexStarling, has been deemed mature enough by Starry Addax to start targeting human rights activists in North Africa,” Talos added.
“The timeline of events including establishing drop points, C2s and building malware since early January 2024 indicates that Starry Addax is rapidly setting up infrastructure to target high value individuals and will continue to gain momentum.”
(The story was updated after publication to include additional insights shared by Cisco Talos.)
