The infamous cybercrime syndicate known as FIN7 has been linked to a spear-phishing campaign targeting the U.S. automotive industry to deliver a known backdoor called Carbanak (aka Anunak).
“FIN7 identified employees at the company who worked in the IT department and had higher levels of administrative rights,” the BlackBerry research and intelligence team said in a new write-up.
“They used the lure of a free IP scanning tool to run their well-known Anunak backdoor and gain an initial foothold utilizing living off the land binaries, scripts, and libraries (LOLBAS).”

FIN7, also known as Carbon Spider, Elbrus, Gold Niagara, ITG14, Sangria Tempest, is a well-known financially motivated e-crime group that has a track record of striking a wide range of industry verticals to deliver malware capable of stealing information from point-of-sale (PoS) systems since 2012.
In recent years, the threat actor has transitioned to conducting ransomware operations, delivering various strains like Black Basta, Cl0p, DarkSide, and REvil. Two Ukrainian members of the group, Fedir Hladyr and Andrii Kolpakov, have been sentenced to prison in the U.S. to date.
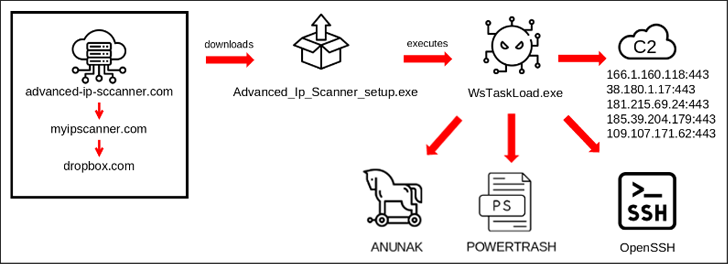
The latest campaign discovered by BlackBerry in late 2023 starts with a spear-phishing email that embeds a booby-trapped link pointing to a bogus site (“advanced-ip-sccanner[.]com”) that masquerades as Advanced IP Scanner.
“This fake site redirected to ‘myipscanner[.]com,’ which in turn redirected to an attacker-owned Dropbox that downloaded the malicious executable WsTaskLoad.exe onto the victim’s machine,” the Canadian cybersecurity company said.

The binary, for its part, initiates a multi-stage process that ultimately leads to the execution of Carbanak. It’s also designed to deliver additional payloads such as POWERTRASH and establish persistence by installing OpenSSH for remote access.
It’s currently not known if the threat actors were planning on deploying ransomware, as the infected system was detected early on and removed from the network before it could reach the lateral movement stage.
While the target of the attack was a “large multinational automotive manufacturer” based in the U.S., BlackBerry said it found several similar malicious domains on the same provider, indicating that it may be part of a wider campaign by FIN7.
To mitigate the risks posed by such threats, it’s recommended that organizations be on the lookout for phishing attempts, enable multi-factor authentication (MFA), keep all software and systems up-to-date, and monitor for unusual login attempts.
