Cybersecurity researchers have warned of a spike in phishing pages created using a website builder tool called Webflow, as threat actors continue to abuse legitimate services like Cloudflare and Microsoft Sway to their advantage.
“The campaigns target sensitive information from different crypto wallets, including Coinbase, MetaMask, Phantom, Trezor, and Bitbuy, as well as login credentials for multiple company webmail platforms, as well as Microsoft 365 login credentials,” Netskope Threat Labs researcher Jan Michael Alcantara said in an analysis.
The cybersecurity company said it tracked a 10-fold increase in traffic to phishing pages crafted using Webflow between April and September 2024, with the attacks targeting more than 120 organizations across the world. A majority of those targeted are located in North America and Asia spanning financial services, banking, and technology sectors.
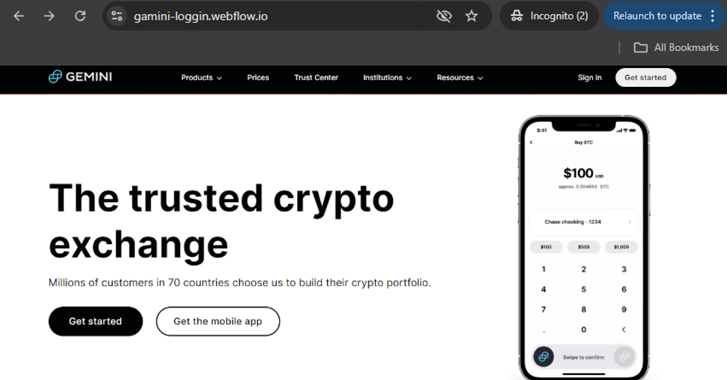
The attackers have been observed using Webflow to create standalone phishing pages, as well as to redirect unsuspecting users to other phishing pages under their control.
“The former provides attackers stealth and ease because there are no phishing lines of code to write and detect, while the latter gives flexibility to the attacker to perform more complex actions as required,” Michael Alcantara said.

What makes Webflow a lot more appealing than Cloudflare R2 or Microsoft Sway is that it allows users to create custom subdomains at no additional cost, as opposed to auto-generated random alphanumeric subdomains that are prone to raise suspicion –
- Cloudflare R2 – https://pub-.r2.dev/webpage.htm
- Microsoft Sway – https://sway.cloud.microsoft/{16_alphanumeric_string}?ref={sharing_option}
In an attempt to increase the likelihood of success of the attack, the phishing pages are designed to mimic the login pages of their legitimate counterparts in order to deceive users into providing their credentials, which are then exfiltrated to a different server in some instances.
Netskope said it also identified Webflow crypto scam websites that use a screenshot of a legitimate wallet homepage as their own landing pages and redirect the visitor to the actual scam site upon clicking anywhere on the bogus site.

The end goal of the crypto-phishing campaign is to steal the victim’s seed phrases, allowing the attackers to hijack control of the cryptocurrency wallets and drain funds.
In the attacks identified by the cybersecurity firm, users who end up providing the recovery phrase are displayed an error message stating their account has been suspended due to “unauthorized activity and identification failure.” The message also prompts the user to contact their support team by initiating an online chat on tawk.to.
It’s worth noting that chat services such as LiveChat, Tawk.to, and Smartsupp have been misused as part of a cryptocurrency scam campaign dubbed CryptoCore by Avast.
“Users should always access important pages, such as their banking portal or webmail, by typing the URL directly into the web browser instead of using search engines or clicking any other links,” Michael Alcantara said.
The development comes as cybercriminals are advertising novel anti-bot services on the dark web that claim to bypass Google’s Safe Browsing warnings on the Chrome web browser.
“Anti-bot services, like Otus Anti-Bot, Remove Red, and Limitless Anti-Bot, have become a cornerstone of complex phishing operations,” SlashNext said in a recent report. “These services aim to prevent security crawlers from identifying phishing pages and blocklisting them.”
“By filtering out cybersecurity bots and disguising phishing pages from scanners, these tools extend the lifespan of malicious sites, helping criminals evade detection longer.”

Ongoing malspam and malvertising campaigns have also been discovered propagating an actively-evolving malware called WARMCOOKIE (aka BadSpace), which then acts as a conduit for malware such as CSharp-Streamer-RAT and Cobalt Strike.
“WarmCookie offers a variety of useful functionality for adversaries including payload deployment, file manipulation, command execution, screenshot collection and persistence, making it attractive to use on systems once initial access has been gained to facilitate longer-term, persistent access within compromised network environments,” Cisco Talos said.
An analysis of the source code suggests that the malware is likely developed by the same threat actors as Resident, a post-compromise implant deployed in as part of an intrusion set dubbed TA866 (aka Asylum Ambuscade), alongside the Rhadamanthys information stealer. These campaigns have singled out the manufacturing sector, followed closely by government and financial services.
“While long-term targeting associated with the distribution campaigns appears indiscriminate, most of the cases where follow-on payloads have been observed were in the United States, with additional cases spread across Canada, United Kingdom, Germany, Italy, Austria, and the Netherlands,” Talos said.