The U.S. government is warning about the resurgence of BlackCat (aka ALPHV) ransomware attacks targeting the healthcare sector as recently as this month.
“Since mid-December 2023, of the nearly 70 leaked victims, the healthcare sector has been the most commonly victimized,” the government said in an updated advisory.
“This is likely in response to the ALPHV/BlackCat administrator’s post encouraging its affiliates to target hospitals after operational action against the group and its infrastructure in early December 2023.”
The alert comes courtesy of the Federal Bureau of Investigation (FBI), the Cybersecurity and Infrastructure Security Agency (CISA), and the Department of Health and Human Services (HHS).
The BlackCat ransomware operation suffered a major blow late last year after a coordinated law enforcement operation led to the seizure of its dark leak sites. But the takedown turned out to be a failure after the group managed to regain control of the sites and switched to a new TOR data leak portal that continues to remain active to date.
It has also ramped up assaults against critical infrastructure organizations in recent weeks, having claimed responsibility for attacks on Prudential Financial, LoanDepot, Trans-Northern Pipelines, and UnitedHealth Group subsidiary Optum.
The development has prompted the U.S. government to announce financial rewards of up to $15 million for information leading to the identification of key members as well as affiliates of the e-crime group.

BlackCat’s ransomware spree coincides with the return of LockBit after similar disruption efforts led by the U.K. National Crime Agency (NCA) last week. Zscaler ThreatLabz said the ransomware gang has updated its encryptor’s ransom notes with TOR URLs pointing to the new infrastructure.
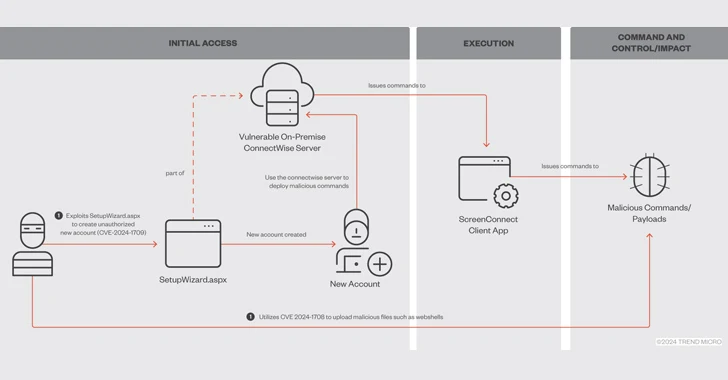
According to a report from SC Magazine, the threat actors breached Optum’s network by leveraging the recently disclosed critical security flaws in ConnectWise’s ScreenConnect remote desktop and access software.
BlackCat, however, has refuted that it used ConnectWise flaws in its attack against Optum. “For all those cyber intelligence so called expert dumbasses we did not use ConnectWise exploit as our initial access so you should base your reports you tell people on actual facts not kiddi speculations,” it claimed.
The flaws, which allow for remote code execution on susceptible systems, have been weaponized by the Black Basta and Bl00dy ransomware gangs as well as by other threat actors to deliver Cobalt Strike Beacons, XWorm, and remote management tools like Atera, Syncro, and even another ScreenConnect client.
The mass exploitation of the two vulnerabilities has also been complemented by adversaries exploiting ScreenConnect and deploying a new Windows variant of KrustyLoader, which was previously spotted as part of a campaign targeting critical vulnerabilities in Ivanti Connect Secure appliances.
Attack surface management firm Censys said, as of February 27, 2024, it observed no less than 3,400 exposed potentially vulnerable ScreenConnect hosts online, with a majority of them located in the U.S., Canada, the U.K., Australia, Germany, France, India, the Netherlands, Turkey, and Ireland.
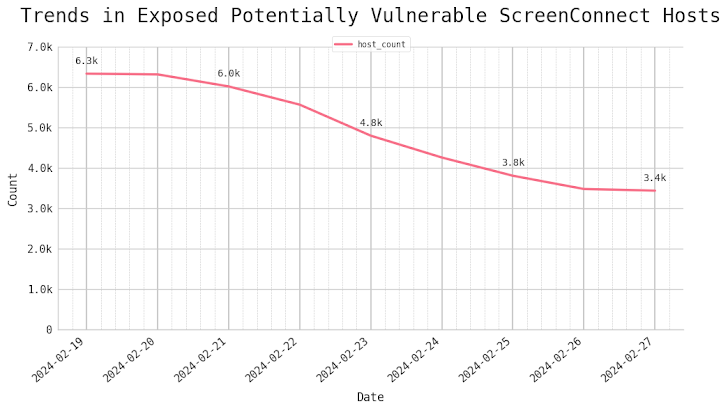
“It’s clear that remote access software like ScreenConnect continues to be a prime target for threat actors,” Censys security researcher Himaja Motheram said.
The findings come as ransomware groups like RansomHouse, Rhysida, and a Phobos variant called Backmydata have continued to compromise various organizations in the U.S., U.K., Europe, and the Middle East.
In a sign that these cybercrime groups are shifting to more nuanced and sophisticated tactics, RansomHouse has been found utilizing a custom tool dubbed MrAgent to deploy the file-encrypting malware at scale.

“MrAgent is a binary designed to run on [VMware ESXi] hypervisors, with the sole purpose of automating and tracking the deployment of ransomware across large environments with a high number of hypervisor systems,” Trellix said. Details of MrAgent first came to light in September 2023.
Another significant tactic adopted by some ransomware groups is the sale of direct network access as a new monetization method via their own blogs, on Telegram channels, or data leak websites, KELA said.
It also follows the public release of a Linux-specific, C-based ransomware threat known as Kryptina, which surfaced in December 2023 on underground forums and has since been made available for free on BreachForums by its creator.
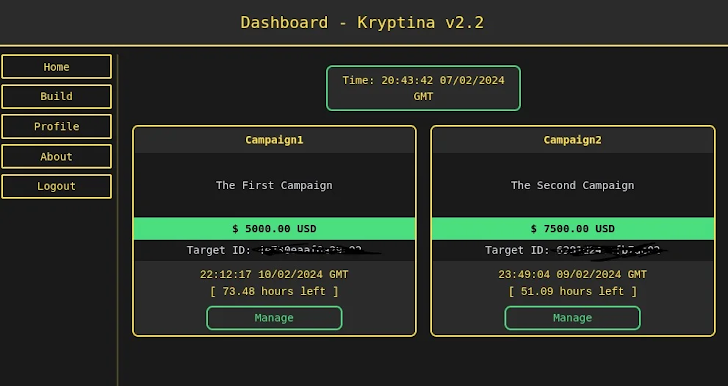
“The release of the RaaS source code, complete with extensive documentation, could have significant implications for the spread and impact of ransomware attacks against Linux systems,” SentinelOne researcher Jim Walter said.
“It is likely to increase the ransomware builder’s attractiveness and usability, drawing in yet more low-skilled participants to the cybercrime ecosystem. There is also significant risk that it will lead to the development of multiple spin-offs and an increase in attacks.”
(The story was updated after publication to include additional information about the exploitation of ConnectWise ScreenConnect flaws.)